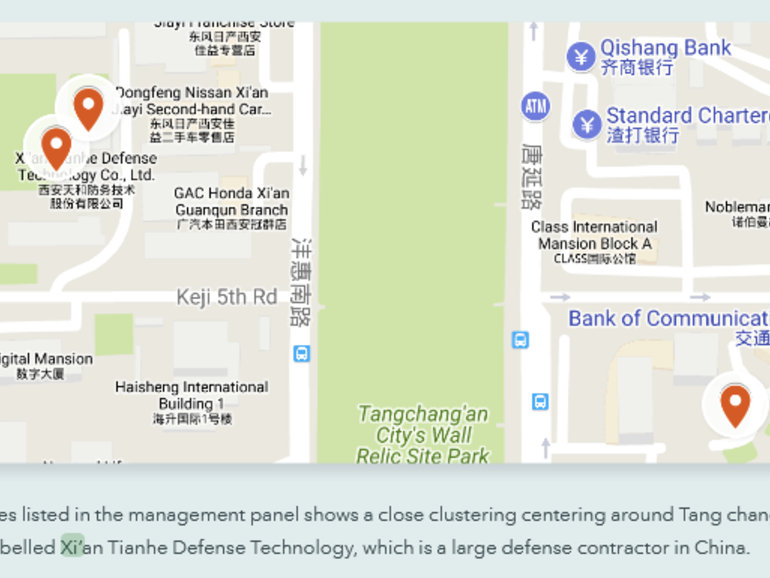
Lookout said it linked APT15 malware to Xi’an Tianhe Defense Technology, a Chinese defense contractor.
In a report published today, cyber-security firm Lookout said it found evidence connecting Android malware that was used to spy on minorities in China to a large government defense contractor from the city of Xi’an.
Lookout’s 52-page report [PDF] details a years-long hacking campaign that has primarily targeted the Uyghur ethnic minority, living in western China, but also the Tibetan community, to a lesser degree.
The campaign infected individuals in these communities with malware, allowing government hackers to keep an eye on the activities of minority communities in China’s border regions but also living abroad in at least 14 other countries.
« Activity of these surveillance campaigns has been observed as far back as 2013, » Lookout researchers said.
The company attributed this secret surveillance to a hacking group they believe operates on behalf of the Chinese government.
Some of the group’s past hacking operations have been documented by other cyber-security firms, and the hacking group is already known in industry circles under different codenames, such as APT15, GREF, Ke3chang, Mirage, Vixen Panda, and Playful Dragon.
The vast majority of past APT15 attacks involved malware designed to infect Windows desktops, but Lookout said the group also developed an arsenal of Android hacking tools.
Hacking tools that were already known include malware strains identified as HenBox, PluginPhantom, Spywaller, and DarthPusher. On top of these, Lookout said it also discovered four new ones, which they codenamed SilkBean, DoubleAgent, CarbonSteal, and GoldenEagle. (see image below for their features)
Source : Connection discovered between Chinese hacker group APT15 and defense contractor
